The Privacy Paradox and Obfuscation

- Jun 9, 2021 modified: Jan, 13 2025
The Privacy Paradox and Obfuscation
protecting privacy in online interactions
privacy paradox:
the discrepancy between an individual's intention to protect their privacy and how they actually behave in the online marketplace.
The clear line between private and public information collection and sharing is becoming quite clouded. While people have become accustomed to sharing their pictures, videos, preferences, stories and other personal information online, a huge amount of online data is collected daily and used by corporations, retailers, criminals, governments, media and private organisations.
Recent university studies reveal that people continue to express serious concerns about privacy and claim it to be an important factor in their online decision-making process.
However,
"Often the relationship between an individual’s intention to disclose personal information and their personal information disclosure behaviours are very different."
obfuscation:
the action of making something obscure, unclear, or unintelligible.
Obfuscation, when properly deployed, can aid in the protection of privacy and in the defeat of data collection, observation and analysis.
Obfuscation... is the 'addition of ambiguous, confusing, or misleading information to interfere with surveillance and data collection projects' to ' buy time, gain cover, and hide in a crowd of signals'.
Finn Brunton & Helen Nissenbaum. Obfuscation: a user's guide for privacy and protest. 2015.

The Privacy Paradox
Privacy is a contentious issue in the debate about consumer behaviour and individual rights. Companies want more customer data while customers say they are reluctant to provide more. And yet studies reveal people are willing to provide more personal data in certain contexts.
Privacy is an important factor in the online decision-making process; however, concern about privacy doesn't match actual online behaviour.
According to several privacy-related studies, the online audience can be divided into three main categories:
1. Privacy fundamentalists: very privacy-oriented and concerned
2. Privacy unconcerned: not at all privacy-oriented
3. Privacy pragmatists: in-between the other two categories
from https://www.keepitusable.com/blog/privacy-paradox-and-how-you-can-use-it-to-increase-conversion/
Consumers are more sensitive about the use of their medical, financial and family information than they are about their product interests, brand preferences or their social media behaviour and usage.
Disclosures of medical, financial and family information or loss of control of this type of information, may lead to security problems, identity fraud or at the very least, social embarrassment.
The Conceptual Model of Disclosure is a theory that states the consumer's behaviour is influenced by their perceived risk of disclosing their information and the trust they have with the company.
The consumer's actual behaviour is most highly influenced by trust. This is why people may disclose information even when they say they're concerned about their privacy.

Obfuscation
Personal data that is shared, bought, sold, managed, analysed and applied will have consequences for our lives.
Your personal information may affect whether you get a loan or a rental lease; if you are an insurance or credit risk; what advertising pop-ups appear on your social media pages or web searches; why companies or services suddenly make contact with you while you are job searching or dealing with mental or other health issues; monitoring of your travels and geographic location at any point in time...et cetera.
Questions we may ask ourselves include -
- "Am I on a list?"
- "Why am I on a list?"
- "How did I get on a list?"
In their academic abstract, Brunton and Nissenbaum explain that their book, Obfuscation: A User's Guide for Privacy and Protest is about obfuscation: the production of noise modelled on an existing signal in order to make a collection of data more ambiguous, confusing, harder to exploit, more difficult to act on, and therefore less valuable.
Obfuscation is a tool for defending and expanding digital privacy against data surveillance, and protesting the unjust collection or misuse of data. The authors provide strategies and an argument for evasion, noncompliance, refusal, even sabotage, particularly for average users not in a position to opt out or exert control over data about themselves.
A practical example of the use of 'obfuscation' can be found during World War Two with the British use of 'chaff'. This was a countermeasure in which aircraft spread a cloud of small, thin pieces of aluminium, metal-glass fibre or plastic, which appeared as a cluster of primary targets on enemy radar screens or swamped the screen with a confusion of multiple returns. This allowed a brief window of time for British war-planes to disrupt enemy radar detection and avoid anti-aircraft fire during air raids.

Bots are scraping your content
Scraper bots can be leveraged to generate more sophisticated phishing campaigns by grabbing product images, descriptions, and pricing information to create counterfeit storefronts or phishing sites aimed at stealing credentials or credit card information.
Dealing with the Privacy Paradox
In dealing with the privacy paradox, companies may try to avoid frustration and the potential consequence of consumer abandonment during a purchase online by using the following strategies to win or improve the trust of consumers.
visible link to a privacy policy
According to studies, the display of a visible link to a 'privacy policy' has a major effect on purchasing behaviour despite only a quarter of the policies being read by the consumer. In most cases, users had more confidence in a site simply because it had a policy.
credit card icons
Even if it does not imply any promise of fraud prevention or privacy protection, consumers find credit card icons reassuring when displayed on a company's webpage and online purchase sites.
show a contact phone number
Consumers revealed a preference for phone information over mailing or email information. They seem to feel reassured when they see a phone number to contact the company if any problems occur during the transaction.

development of policy simplifications and standardised indicators
Just having a link to a privacy policy makes a difference to a potential consumer, especially through the application of standardized, simple visual indicators. It is the presence of a policy that has a positive effect on users, not its content. Users are looking for "trustworthiness" not solely based on fact, but on appearance and first impressions.
adapted from https://www.keepitusable.com/blog/privacy-paradox-and-how-you-can-use-it-to-increase-conversion/
Defeating Digital Surveillance
Brunton and Nissenbaum maintain that obfuscation has a role to play, not as a replacement for governance, business conduct, or technological interventions, or as a one-size-fits-all solution but as a tool that fits into the larger network of privacy practices.
In particular, it's a tool particularly well suited to the category of people without access to other modes of recourse, whether at a particular moment or in general—people who, as it happens, may be unable to deploy optimally configured privacy-protection tools because they are on the weak side of a particular information-power relationship.
The focus is on mitigating and defeating present-day digital surveillance by adding concepts and techniques to an existing and expanding toolkit...
for evasion, noncompliance, outright refusal, deliberate sabotage, and... depending on the adversary, the goals, and the resources, we provide methods for disappearance, for time-wasting and analysis frustrating, for prankish disobedience, for collective protest, for acts of individual redress both great and small.
Brunton and Nissenbaum's aim is to enrich the reader's understanding of obfuscation by considering why obfuscation has a role to play in various forms of privacy work; the ethical, social, and political problems raised by using obfuscatory tactics; and ways of assessing whether obfuscation works, or can work, in particular scenarios.
They recognise that digital noise can be destructive or productive and on a variety of scales:
Platforms and channels can be swamped by code that mimics and distorts human communication - bots, like-farmers, decoys and hydras. Other tools, like the anonymous Tor browser, the Guardian's SecureDrop, or stylometric obfuscation (to disguise authorship), can be mission-critical for dissidents.
The authors advise that there is an ever growing demand for consumer-focused privacy-preserving apps, like CacheCloak, which hides mobile locations in a spaghetti map of plausible trails, or
FaceCloak, which gives a layer of control over personal data within Facebook.
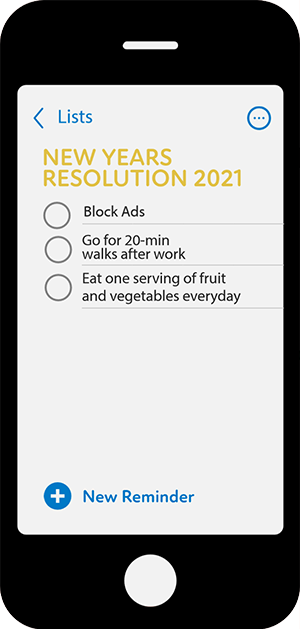
When Apple rolled out the latest version of its iOS operating system, it allowed iPhone and iPad owners to download apps that block digital advertisements on their phones. Since April 2021, advertisers have not been able to track iPhone users around the internet without their explicit consent.
Hostilities with Facebook are about to be renewed as Apple is expected to place higher barriers around Apple products when the iOS 15 platform hits the market in mid-2021. This will make it even more difficult for Facebook to collect data from its 2.9 billion monthly users. It may cause the social media group to lower charges for targeted advertisements.
Newspapers, magazine and online publishers and social media giants acknowledge ad-blocking as a threat, but claim they are equipped to handle it.
Nissenbaum says the Ad-blocking wars that have led to legal threats by online publishers "is a devilish move by ad networks to conflate the massive back-end of tracking, aggregation, mining and profiling with advertising itself." She concludes:
"Our effort, both with TrackMeNot and AdNauseam, has been targeted at the former [ad networks]. I don't love advertising but I can tolerate it. When supporters of the current structures of behavioural advertising say this will be the end of all the innovation and free stuff on the web, our response is: no. Although this might happen if advertising itself goes away, it does not require the back-end tracking for survival."
War and Privacy

The arm wrestle between people desiring stronger privacy protections who resort to obfuscation as a tool to assist them, and the desire of advertisers to access important private data for their commercial use is certain to continue.
"By mapping out obfuscation tools, practices, and goals, Brunton and Nissenbaum provide a valuable framework for understanding how people seek to achieve privacy and control in a data-soaked world."

When we more fully understand our behaviours as consumers within the 'Privacy Paradox' framework; for example, actually reading 'privacy polices’, and then comprehend the potential power we have to disrupt unwanted personal data collection through the application of 'Obfuscation’ techniques, many of us (especially the most vulnerable in society) will no longer be exploited or intimidated by data collectors, whether they are government or private entities.
Obfuscation practices by internet users, combined with Apple’s intention to make privacy and security key features of their products, may force the antagonists and protagonists that have emerged in the 'ad-blocking wars' to eventually learn to walk hand-in-hand.
It all comes down to trust.
Researched, compiled, composed, written & edited by Dr Steve Gration, June 2021
REFERENCES & SOURCES
https://we.riseup.net/assets/355198/Obfuscation.pdf
Boyd D. It's Complicated: The Social Lives of Networked Teens. Yale University Press, 2014.
Brunton F. & Nissenbaum H. Obfuscation: A User’s Guide for Privacy and Protest. MIT Press, USA 2015.
https://mitpress.mit.edu/books/obfuscation
https://www.keepitusable.com/blog/privacy-paradox-and-how-you-can-use-it-to-increase-conversion/
https://www.theguardian.com/technology/2015/oct/24/obfuscation-users-guide-for-privacy-and-protest-online-surveillance
https://mitpress.universitypressscholarship.com/view/10.7551/mitpress/9780262029735.001.0001/upso-9780262029735?rskey=S9xUCK&result=4
https://www.theguardian.com/media/2015/sep/20/ad-blocking-threat-publishers-apple-ios9
Search News Articles...
Recent Articles

Your IP Address and SEO
- Mar 06 2026
- /
- 290

Keywords no longer as visible in GSC
- Jan 12 2026
- /
- 851

Unique Web Systems Matter in a World of Sameness
- Dec 26 2025
- /
- 632

Most AI Websites Fail to Rank
- Nov 18 2025
- /
- 951

Sitemap.xml Best Practices
- Oct 14 2025
- /
- 3596

Fake Reviews on Google My Business
- Oct 07 2025
- /
- 897

Sending Emails from Code
- Sep 17 2025
- /
- 968

US Tariff Shifts Undermining eCommerce
- Sep 05 2025
- /
- 1153

Small Business Success Formula
- Aug 23 2025
- /
- 844

Do Strong CTAs Help or Hurt Your Website?
- Jul 31 2025
- /
- 1084
View All News Articles
Categories
A Gold Coast SEO and Web Developer